What is the darknet? Shrouded in mystery for many years and often associated with ominous connotations, the darknet is a part of the internet that evokes curiosity, fascination, and even fear in many people.
This “hidden” part of the web isn’t accessible without special software. Contrary to popular belief, it’s not just used by criminals. Some people use the darknet to protect their privacy or to express their opinions freely. Others take advantage of the TOR network’s anonymity for different reasons, which can range from questionable to illegal activities.
Within the darknet, one can find an underworld catering to those looking to trade illegal goods or software. Additionally, it hosts groups offering RaaS (Ransomware as a Service) solutions and activists fighting against censorship or surveillance.
It’s also worth noting that many social media platforms, such as Facebook and X, have their own addresses on the TOR network. Entering the darknet is like stepping into a world where the lines between good and evil blur, and the possibilities are vast.
How does TOR software work? Is the darknet solely a breeding ground for cyber threats? How can we protect our applications from connections via TOR?
We will address these and many other questions in the following sections of the article.
The differences between the Darknet and the traditional Internet are significant and crucial for understanding the unique nature of this “world.”
Here are some key distinctions:
To start, it’s essential to understand where the darknet is positioned within the broader network. The internet can be divided into the Surface Web, also known as the clearnet, which is the space you navigate daily when browsing social media, searching for information, or shopping online. This is the part of the internet you are very familiar with—it’s worth noting that the Surface Web is often indexed in search engines, meaning it’s easy to find various websites using specific keywords.
The second part of the internet is the so-called Deep Web, which is deeply hidden. However, this isn’t yet the mysterious network often discussed. The Deep Web includes all websites and forums that are not indexed (such as private forums whose addresses can’t be found through a Google search). This part of the web also includes scientific reports, government materials, databases, and other information that cannot be accessed simply by entering keywords.
The third and final “layer” of the internet is the Dark Web, also known as the Darknet. This includes all websites, forums, and marketplaces hidden behind the TOR network (as mentioned earlier, these sites are not necessarily illegal). You cannot access this part of the internet using familiar web browsers, and the addresses do not resemble those found on the clearnet.
The following iceberg illustration effectively depicts the outlined structure:
One of the key differences between URLs on the regular internet and those on the darknet is the TLD (top-level domain). Unlike common TLDs like .com, .pl, or .org, the darknet uses a pseudo-top-level domain that is not listed in the official TLD registry: .onion. As you might guess, the .onion domain comes from “Onion Routing,” the method used to ensure anonymity.
Additionally, URLs on the darknet do not form readable words. For example, the TOR project’s address on the clearnet is a typical link:
https://www.torproject.org/
For comparison, a v3 onion address looks like this (in reality, it’s the same site):
http://2gzyxa5ihm7nsggfxnu52rck2vv4rvmdlkiu3zzui5du4xyclen53wid.onion/
This address is composed of 56 random characters and cannot be purchased like regular domains. The link is generated based on the computer’s processing power using the ed25519 algorithm. While there are methods to create an address with specific starting characters, this requires significant time and computational resources.
It’s important to note that, unlike regular domains, which typically point to an IP address that can identify the server hosting the domain, every TOR network address points to 127.0.0.1.
Maximize your email deliverability and security with EmailLabs!
On the “regular” internet, you can use standard web browser like Chrome, Firefox, or Opera to search for popular sites or browse social media. However, when it comes to accessing the TOR network, you can still use these browsers, but they need to be “slightly” modified with the Tor software.
Alternatively, there’s the Tor Browser (based on Firefox), which allows direct users access to the TOR network. The Tor software itself is a command-line application that doesn’t enable direct browsing of the TOR network on its own.
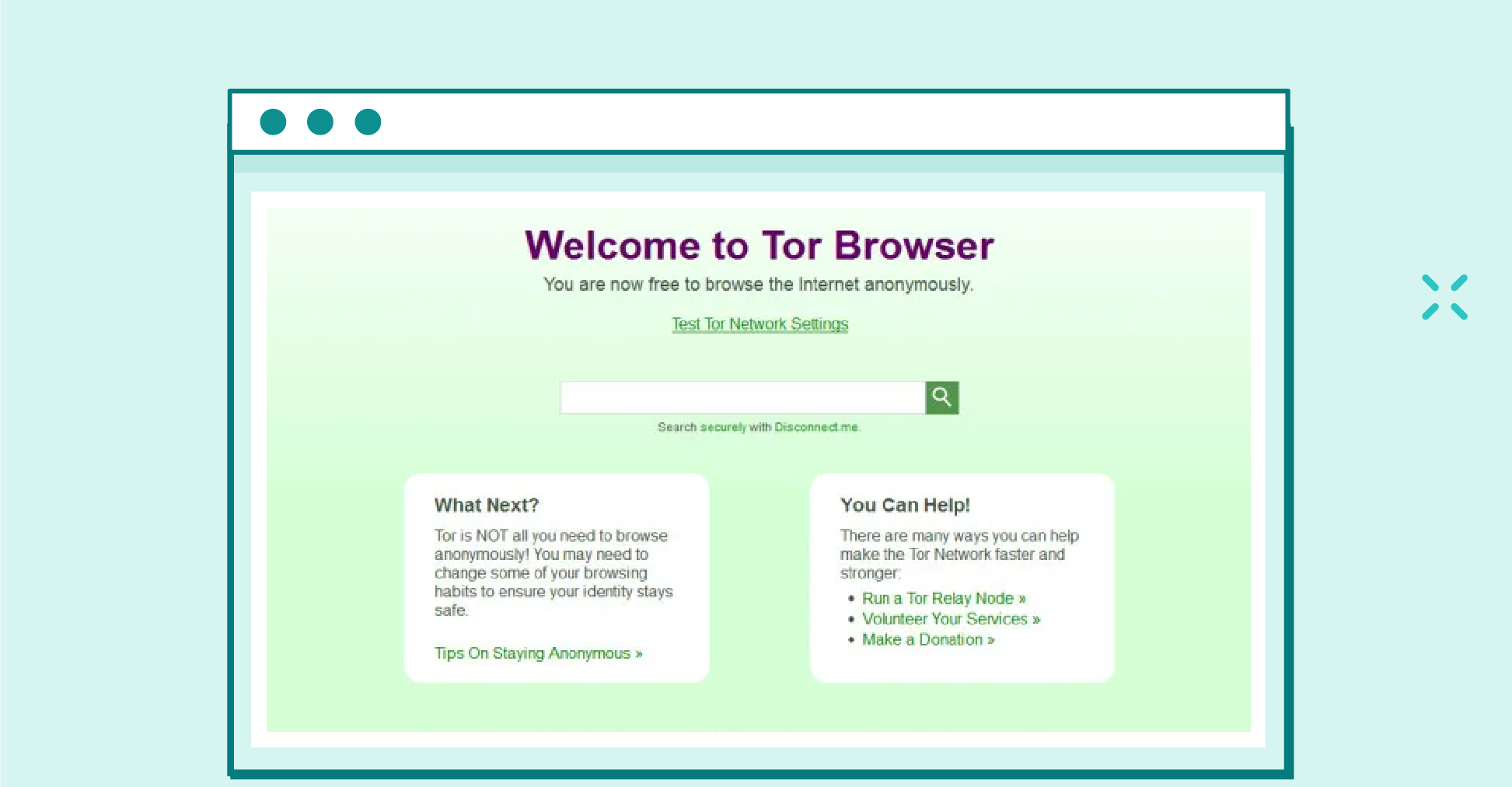
The Tor Browser is a web browser designed for privacy and anonymity online. It is built on a modified version of Mozilla Firefox and routes your internet traffic through the Tor network, a decentralized network of volunteer-operated servers. This process, known as “onion routing,” encrypts your data multiple times and passes it through several nodes (or relays) before reaching the final destination.
To understand the phenomenon of the TOR network and why various social groups so widely use this software, it’s essential to grasp how TOR works—specifically, The Onion Router.
The Onion Router, commonly known as TOR, gets its name from the onion because the entire connection is literally multi layered encryption. In a typical public internet, the process works by having users connect to the destination server through their Internet Service Provider (ISP). Simplifying it further, our computer connects directly to the address we want to reach, and this connection is usually not encrypted.
When discussing the TOR network, we must highlight three main components:
It’s important to note that the actual operation of the TOR network is far more complex, and the description provided here is intended to give you a basic understanding of this fascinating network.
Below is a graphical representation of the TOR network:
You might wonder if it’s possible to track these servers to monitor who is connecting to what and from where.
The answer is: Unfortunately, it’s not that simple.
Nodes are randomly selected during each connection, so it’s unknown which servers the traffic will pass through until the moment of connection.
The image below illustrates an example of a route to a site within the TOR network:
Anyone can set up these nodes (though it’s important to remember that with exit nodes, all traffic exits through “your” server, which can lead to legal issues if the connection is used for illegal activities).
According to TOR metrics, there are currently around 8,000 nodes and about 2,000 bridges (which we haven’t covered in this article) worldwide. The number of nodes and their locations change very dynamically, and since anyone can create these nodes, the network continuously expands, providing an anonymous space for various groups.
Unless there are OPSEC (Operational Security) failures, tracking TOR users would require controlling the majority of the servers to correlate traffic across all nodes. As we recall, the entry node “knows” where the connection originates, while the exit node has information on the destination. However, given the current dynamics, this is not feasible at this time.
As we’ve learned, the TOR network’s unique functionality has won over many people who seek privacy protection and anonymity online (though it’s important to note that achieving full anonymity requires attention to many other factors not covered here).
Consequently, this software is used not only by cybercriminals but also by individuals who value their anonymity (it’s essential to remember that wanting to maintain anonymity does not equate to being a cybercriminal). Many of today’s social media platforms, email applications, and even chat services for discussing personal issues have their own addresses within the TOR network.
A prime example of this is the popular Facebook:
TOR is not just a tool for criminals—although it is often associated with them (more on that later in the article).
This software is frequently used by journalists, activists, and regular users who want to protect their data from surveillance. Today, many non-profit organizations and projects dedicated to defending free speech and privacy also rely on TOR technology. As with many other tools, its ethical use depends on how it is applied.
As mentioned earlier, the ethical use of tools, including the TOR project, depends on how they are utilized. On one hand, TOR can be used to maintain anonymity in oppressive regimes; on the other hand, it is also frequently used by cybercriminals.
Due to the nature of the network, various criminal groups use the dark web sites to sell malware or share data leaks from different sites. Additionally, you’ll find websites for numerous ransomware groups (often operating under the Ransomware as a Service model), such as the recently notorious LockBit.
Additionally, cybercriminals operate numerous illicit forums on this network, all within an environment that provides significant anonymity. However, TOR is not just used for browsing sites accessible only within this network. A key aspect of TOR is its ability to route traffic from virtually any software through it.
It allows them to obscure their real IP address when running tools like vulnerability scanners, so the logs will only show the IP address of the exit node, not the attacker’s actual IP. Similarly, criminals can use the TOR network for data exfiltration or communication with Command and Control (C2) servers.
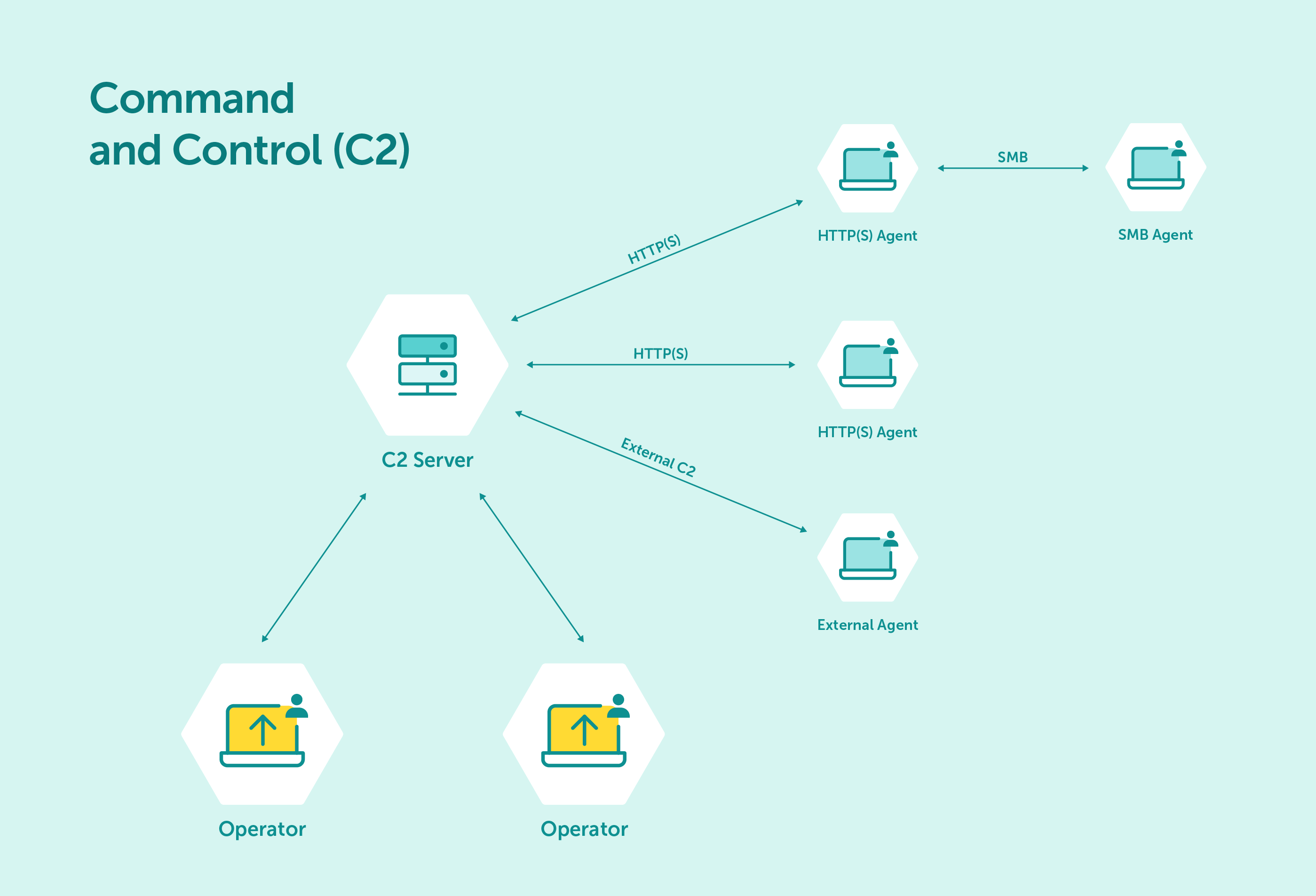
source: https://havocframework.com
The reason cybercriminals use TOR for their activities is essentially the same reason why “ordinary” people use it—it provides a high level of anonymity from the outset.
Of course, cybercriminals often enhance this anonymity by using various VPNs and specialized operating systems that route all traffic through TOR. This makes them very difficult to track, assuming no other human errors occur. However, it’s not impossible. Law enforcement agencies, such as the Central Cybercrime Bureau, have successfully apprehended individuals using TOR. It’s important to note that in these cases, it wasn’t TOR itself that failed; rather, it was other factors.
Maximize your email deliverability and security with EmailLabs!
As we already know, the darknet enables users to maintain a high level of anonymity by hiding real IP addresses and other digital footprints. On the darknet, you can find many forums where cybercriminals share guides or leaked databases. There are also marketplaces where, for a fee, one can commission a hacking service or purchase ready-made malware (with all transactions conducted using cryptocurrencies). Additionally, it’s an ideal environment where cybercriminals use TOR-based communication platforms to plan and coordinate their activities.
But how does the darknet contribute to the growth of cybercrime? What factors are driving the increase in cyberattacks, and how does the darknet play into this?
The answer is quite simple, but before we get to it, let’s take a step back a few years…
Not too long ago, conducting a successful hacking attack and infecting a large number of devices required at least some technical skills. Back then, while it was possible to buy malware on certain forums, the majority of infections and attacks were carried out by individuals with some level of experience.
Today, cybercrime has evolved into a business model, most notably recognized as Ransomware as a Service or Phishing as a Service. These are services where individuals with no knowledge of hacking or creating malware can, for a fee, access a dedicated platform for activities like phishing. These platforms provide everything needed, including payment gateways, message templates, and phishing websites.
An offer created by the above panel imitating a well-known Polish retailer.
When it comes to ransomware, you can also purchase software ready for distribution, without worrying about updates. Interestingly, there are also so-called brokers who sell access to various networks. This means that with enough money, you can acquire malicious software and purchase access to a company or platform to carry out a malicious campaign.
There may be situations where you want to block traffic from the TOR network to your web applications. This decision might be based on a risk assessment, where you determine that most traffic from this network could be associated with malicious online activity.
There are several ways to block this traffic. One option is to use ipset, which can maintain an updated list of exit nodes. Such a list can be found on sites like FireHOL. It’s important to note that the list of exit nodes changes frequently, so it needs to be regularly updated. If you use a service like Cloudflare, you can create a policy that detects all connections from TOR. In this case, I recommend checking the documentation for detailed instructions.
Remember that cybercriminals don’t have to connect directly to your applications via TOR. They might use services like RDP or VPN to connect from an IP address that ultimately appears legitimate.
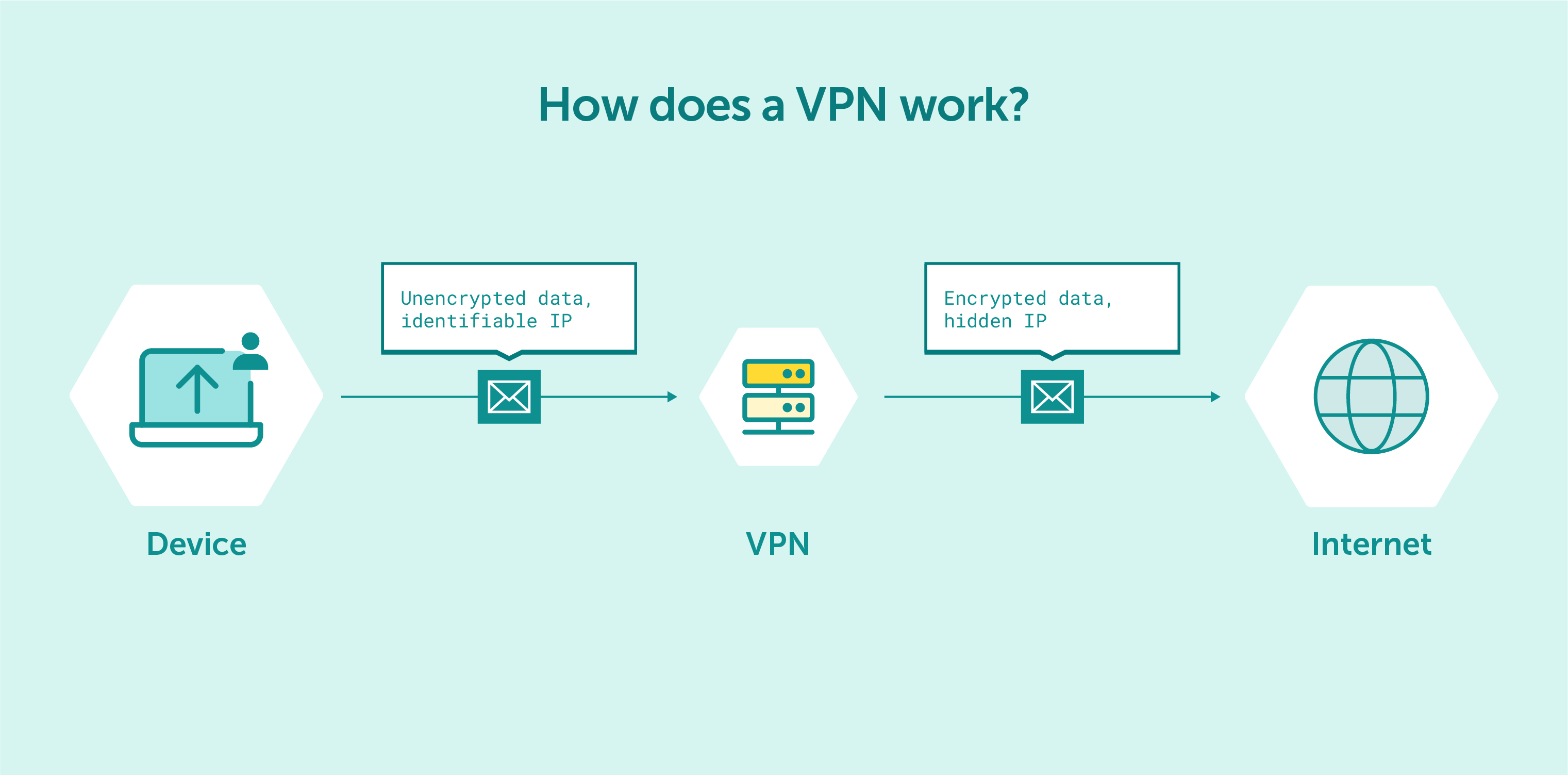
The primary purpose of a VPN is to protect your online privacy, secure your data, and allow you to access resources and websites as if you were connected to a private network, regardless of your physical location.
On the previously mentioned FireHOL website, you can also find IP lists for various other anonymization services. If you want to protect yourself against such connections (at least to a significant extent), it’s worth considering importing these lists into your security solutions.
To conclude this article, it’s important to debunk three common myths related to the darknet and the TOR network:
Stay Secure 👾!
We live in a world where your customers switch seamlessly between laptops, smartphones, and tablets. They navigate a complex digital ecosystem – checking emails, using mobile apps, and reacting...
We are delighted to announce that Vercom S.A., the company behind the EmailLabs project, has successfully completed the ISO 22301 certification process. This significant achievement underscores our commitment to...
EmailLabs, as part of the Vercom group, proudly announces its full commitment to aligning its ICT services with the latest cybersecurity standards. In response to dynamically changing regulations, the...
We are pleased to announce that MessageFlow, a product from the Vercom S.A. group, has received the prestigious CSA (Certified Senders Alliance) Certification. This recognition not only underscores the...
Best practices, Maile marketingowe, Marketing E-mails, Transactional Emails
Mass email sending is a critical strategy for business owners, marketers, developers, and nonprofit managers looking to scale their outreach. Whether you are announcing a new product feature, distributing...
Best practices, Marketing E-mails
Customer feedback is the fuel for business growth, but gathering it effectively requires more than just a list of questions. Email surveys remain the most direct channel for understanding...
Best practices, Email Marketing, Pytania i odpowiedzi
Mail merge combines a template document with data to create personalized communications. This technique saves time by automatically generating individualized letters, emails, and labels without manual entry. What Is...
Best practices, Maile marketingowe, Marketing E-mails, Transactional Emails
Mass email sending is a critical strategy for business owners, marketers, developers, and nonprofit managers looking to scale their outreach. Whether you are announcing a new product feature, distributing...
Best practices, Marketing E-mails
Customer feedback is the fuel for business growth, but gathering it effectively requires more than just a list of questions. Email surveys remain the most direct channel for understanding...
Best practices, Email Marketing, Pytania i odpowiedzi
Mail merge combines a template document with data to create personalized communications. This technique saves time by automatically generating individualized letters, emails, and labels without manual entry. What Is...
IT & Tech, Pytania i odpowiedzi, Technical
When an email travels from sender to recipient, it passes through several critical components of email infrastructure. At the heart of this journey sits the Mail Transfer Agent (MTA)...
Best practices, Deliverability, Google and Yahoo's Requirements, Pytania i odpowiedzi
The world of email marketing is constantly evolving, and leading mail service providers – Gmail, Yahoo, Microsoft, and Apple – regularly update their guidelines for senders. In recent years,...
Gmail, Google and Yahoo's Requirements
You might have noticed a new item in your Gmail sidebar recently – the “Manage subscriptions” tab, often flagged with a blue notification dot. While Google announced this feature...
IT & Tech, Pytania i odpowiedzi, Technical
Efficient email communication isn’t just about sending messages — it also involves integrating email functionality into your business systems and applications. Email APIs (Application Programming Interfaces) serve as the...
One of the most important yet often underestimated elements in shaping a company’s brand perception is the transactional email. In e-commerce, the design of such messages must be carefully...
Google and Yahoo's Requirements, Yahoogle
2024 brought fundamental changes to email marketing, introducing new, stringent requirements for senders. Since February 1, 2024, Google and Yahoo have started enforcing new deliverability rules, primarily targeting bulk...