Best practices, Best practices, Email Authentication
Best practices, Best practices, Email Authentication

DKIM2 is not a minor DNS configuration update. It is a systemic response to two critical business problems:
The standard is progressing through the IETF drafting process considerably faster than originally anticipated. First deployments at major mailbox providers are forecast for the end of 2026. Full ecosystem rollout will take longer, but the direction of travel for authentication protocol architecture is now clearly set.
The email infrastructure of most organizations operating in business or transactional sending models relies on DKIM. Defined in RFC 6376 and published in 2011, DKIM is an authentication mechanism built on asymmetric cryptography.
During sending, the originating mail server computes a cryptographic hash (a fixed-length mathematical fingerprint) derived from a defined set of message headers and the message body. Even a single-character change to the original content produces an entirely different hash value. The server then encrypts that hash using its private key, producing the DKIM signature that is inserted as a message header. The corresponding public key is published in the sending domain’s DNS records.
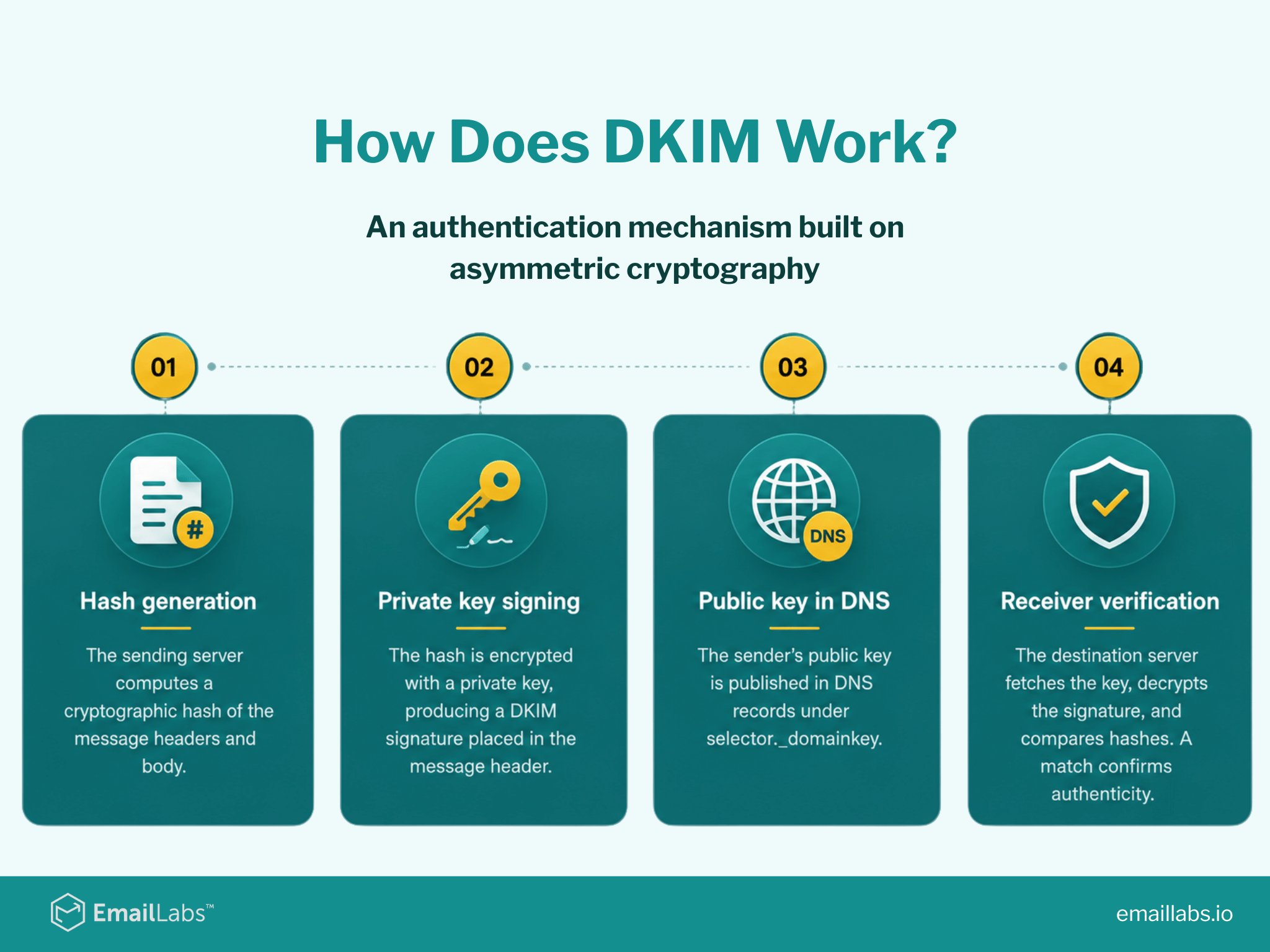
When the message reaches its destination, the receiving infrastructure retrieves the public key from DNS, decrypts the signature, and independently computes its own hash of the received message. If the two hash values match, the receiving system has confirmed two things: the message genuinely originated from the domain that signed it, and it was not altered in transit.
DKIM does not, by itself, block or authorize message delivery. It functions purely as a signal. The delivery decision rests with DMARC policy, which evaluates the DKIM verification result alongside domain alignment in the From header before enforcing the sender’s declared policy.
After more than a decade of operating the current DKIM standard across the global email ecosystem, the industry has identified structural weaknesses that cannot be remedied without a fundamental redesign of the protocol.
In enterprise environments, it is routine for messages to be relayed to external mailboxes via internal forwarding systems. The same challenge arises with automated mailing lists (including corporate distribution groups) that modify messages in transit, whether by prepending tags to subject lines or appending mandatory legal footers to message bodies.
In either case, the content or headers of the message are altered. A change to even a single character causes the receiving system to compute a completely different cryptographic hash, which immediately invalidates the original DKIM signature. The message is flagged as having been tampered with, even though the modification was entirely legitimate.
In 2019, the ARC (Authenticated Received Chain) protocol was introduced as a stopgap. ARC allows intermediary servers to attest that a message passed authentication checks before it was modified. The mechanism has significant limitations, however. ARC provides no standardized method for the final receiver to assess the trustworthiness of the entity adding the ARC signature, and there is no way to verify precisely what was changed. Furthermore, on April 22, 2026, the IETF DMARC Working Group submitted draft-ietf-dmarc-arc-to-historic-00, which formally proposes reclassifying ARC as a historic standard.
The official verdict is clear: the problem ARC was designed to solve (preserving authentication context across successive forwarding nodes) remains unresolved. The cause of failure was the lack of consensus on a trust model among intermediaries, as the ecosystem never agreed on whose ARC signatures should actually be trusted. Implementers are receiving a clear signal to cease deploying this protocol. DKIM2 is therefore not an alternative to ARC, but its designated successor, building the lessons learned from the ARC experiment directly into the protocol’s architecture.
The current DKIM standard signs a message but does not bind that signature to a specific recipient or to the SMTP envelope data. This is a critical security gap. An attacker who intercepts a legitimately signed email (a newsletter sent to an opted-in subscriber, for example) can redistribute it to millions of unauthorized recipients.
Because DKIM attests only to the identity of the sending domain, not to the intent or intended destination of the message, the signature remains valid at every receiving system that checks it.
The result is that the sender’s domain accumulates a spam reputation for messages it never generated. This is not a theoretical attack vector. It is a technique actively exploited in large-scale spam operations.
DKIM2 is a proposed standard developed within the IETF Working Group on DKIM. Its objective is the complete replacement of the current DKIM standard, not an extension of it. The architectural foundation is preserved: senders cryptographically sign messages, and verifiers retrieve the public key from DNS. Every other layer of the protocol has been redesigned.
The current working document is designated draft-ietf-dkim-dkim2-spec-01. The specification is authored by engineers from three of the largest organizations in the email ecosystem: Richard Clayton (Yahoo), Wei Chuang (Google), and Bron Gondwana (Fastmail).
The involvement of engineers from these organizations signals that this is an operationally motivated initiative, not an academic exercise. These are infrastructure operators processing tens of billions of messages per day, which means the standard is being designed against real-world load and production requirements.
Official draft: datatracker.ietf.org/doc/draft-ietf-dkim-dkim2-spec/
Implementation status (May 2026): The standard has already passed its first real-world validation. Engineers at SocketLabs completed a successful interoperability test in which a message signed according to the latest working draft was transmitted from SocketLabs infrastructure and correctly verified by an independent mailbox operator’s test system.
This was the first publicly confirmed end-to-end transmission between independent production systems, documented by the SocketLabs engineering team. The pace of development is outrunning early projections, and industry participants are forecasting deployed code at major mailbox providers before the end of 2026.
Under the current DKIM standard, a message carries a single signature. Verification is binary: the signature either holds or it does not. DKIM2 replaces this model entirely. Every server that handles a message in transit adds its own signature, tagged with a sequential index number: i=1 (the original sender), i=2 (the first intermediary), i=3 (the next hop), and so on. A gap in this sequence is treated by receiving systems as the equivalent of no signature at all.
From an operational standpoint, this gives the receiving infrastructure full visibility into not just the identity of the original sender, but every server in the delivery chain. Each node can be independently assessed and assigned its own reputation score. This chain-of-custody structure is the architectural foundation on which every other DKIM2 security mechanism is built.
Below is a simplified model showing two chained signatures (the original sender and a mailing list server) and how they interlock:
DKIM2-Signature: i=1; d=sender.example; t=1711497600; [email protected]; [email protected]; s=sel1:ed25519-sha256:xyz789… DKIM2-Signature: i=2; d=mailinglist.org; t=1711497660; [email protected]; [email protected]; s=sel2:rsa-sha256:uvw321…
The mf= value in signature i=2 corresponds exactly to the rt= value in signature i=1. This creates a coherent, cryptographically sealed chain of custody. The verifier at the receiving end has full visibility into the authenticated route the message traveled.
Business context: Corporate forwarding systems, security appliances, and mailing lists routinely modify messages in transit. Under the current DKIM standard, any such modification irreversibly invalidates the original signature. Under DKIM2, every server that modifies a message is required to precisely document what it changed.
Technical mechanism: This documentation is implemented through a new Message-Instance header containing an r= tag that carries instructions encoded as Base64-encoded JSON. These instructions, referred to in the specification as recipes, describe the modifications made with sufficient precision that a downstream verifier can mathematically reverse them and verify all earlier signatures in the chain. Each successive Message-Instance header carries a unique revision number (m=1, m=2, …).
The JSON structures can describe both header modifications (such as prepending a [List] tag to the subject line) and body changes (such as appending a mandatory footer). If reconstruction of the original is technically impossible, the intermediary server declares this explicitly by sending a null value, and the trust decision falls to the verifier’s local policy. Verifiers do not process the full chain on every message. If the message structure has not changed, verification is limited to checking the final signature. Full reconstruction is triggered only when modifications are detected (a deliberate computational optimization at scale).
Business context: A replay attack is one of the most damaging threats to the reputation of a sending domain. A properly signed, authorized campaign sent to a legitimate subscriber list can be intercepted and redistributed to millions of unauthorized addresses. Under the current DKIM standard, that message retains a valid cryptographic signature. Spam filters see an authenticated, reputable domain, and the domain’s deliverability suffers for spam it never sent.
Technical mechanism: DKIM2 addresses this through envelope binding: cryptographically tying each signature to the SMTP envelope data of that specific transmission. Every DKIM2 signature is required to include two new tags: mf= (the MAIL FROM address, Base64-encoded) and rt= (the RCPT TO addresses). A message signed for [email protected] that arrives at [email protected] will trigger immediate detection of the mismatch and rejection by the verifying server.
DMARC monitoring implications: The strict envelope binding and the logging of every intermediary in the delivery chain significantly complicates DMARC analytics. Rendering the message path through multiple hops in a way that remains readable and actionable is a genuine product design problem for monitoring tool vendors. Organizations using DMARC analytics platforms should engage their vendors early on DKIM2 roadmap plans.
The replay protection mechanism is complemented by a set of sender intent flags, declared in the f= tag of the signature:
| Flag | Type | Meaning |
|---|---|---|
| donotexplode | Request | Instructs intermediaries not to redistribute this message to multiple recipients |
| donotmodify | Request | Instructs intermediaries not to modify the message in transit |
| exploded | Declaration | Signals that this message is being distributed to multiple recipients (e.g., via a mailing list) |
| feedback | Request | Requests delivery quality feedback from the receiving system |
Business context: Backscatter is the phenomenon in which a sending domain receives large volumes of non-delivery notifications for messages it never generated. In a typical backscatter scenario, a spammer forges the sender address. When the target mail server rejects the message, it sends a non-delivery report to the innocent domain whose address was forged, generating both an infrastructure burden and a negative reputational signal.
Technical mechanism: Under DKIM2, DSN (Delivery Status Notification) messages must be routed exclusively to the server that physically transmitted the message being reported. That address is derived from the mf= tag in the final signature of the cryptographic chain, not from an arbitrarily declared Return-Path header that may have been forged. Additionally, when mf=<> (an empty tag, the convention for DSN messages themselves), the protocol blocks the generation of further bounce messages at the protocol level, terminating bounce loops immediately.
Infrastructure implications for ESP and CPaaS platforms: In a DKIM2 ecosystem, major mailbox providers will have the cryptographic assurance needed to safely resume asynchronous DSN delivery in cases where today they prefer silent drops or deferrals. For email infrastructure providers and CPaaS platforms, this means an inevitable increase in inbound bounce volume that will require infrastructure planning. Platforms currently relying on manual bounce handling need to factor this into their 2026 and 2027 infrastructure roadmaps.
Secure asynchronous DSN handling also carries a deeper implication for compliance operations. Because a bounce is routed back to the server that physically handled the outbound message, ESPs gain cryptographically verified attribution: identifying precisely which sender in their infrastructure generated a complaint or rejection. Today’s list suppression and complaint-handling logic frequently relies on heuristics and inference. DKIM2 creates the conditions for considerably more precise and defensible implementation.
A key note for teams planning migration: The current draft leaves cryptographic key formats unchanged. DKIM2 keys are stored under the same DNS records as current DKIM (selector._domainkey.domain), and the key structure is identical. The sender-side infrastructure rework required for DKIM2 will be considerably less disruptive than a clean-sheet protocol migration might suggest.
DKIM2 authentication keys are stored under the same DNS namespace as the current DKIM standard (selector._domainkey.domain). Existing DNS infrastructure, key management tooling, and established rotation procedures can be carried over directly. This is a deliberate architectural choice to reduce the migration barrier for mail system administrators.
DKIM2 also introduces a formal framework for feedback loops. Declaring the f=feedback flag in a signature signals that the sending system is requesting delivery quality feedback from the receiver. The specific reporting format will be defined in a companion document.
| Feature | DKIM | DKIM2 |
|---|---|---|
| Signatures | One or many, independent | Ordered chain (i=1, 2, …) |
| SMTP envelope | Not signed | Bound via mf= and rt= |
| Forwarders and mailing lists | Modifications break signatures | Recipes enable reconstruction of changes |
| Replay attacks | No protection | Recipients cryptographically bound to signature |
| Backscatter / DSN | No mechanism | Bounce routed back through signature chain |
| Signed headers | Manual list (h=) | All headers by default |
| Cryptography | RSA-SHA256, Ed25519 optional | RSA-SHA256 and Ed25519 mandatory |
| ARC protocol | Required as a workaround | Rendered obsolete |
| Version tag | v=1 | Absent (intentional design decision) |
| DNS namespace | selector._domainkey.domain | Unchanged: full backward compatibility |
From the perspective of organizations running high-volume transactional or marketing email programs, DKIM2 carries four strategic operational consequences.
First, improved deliverability in B2B environments. Enterprise mail gateways, forwarding systems, and CRM integrations are currently among the leading causes of DKIM signature failures. In a DKIM2 ecosystem, each intermediary server adds its own signature and documents its changes precisely. The result is a meaningful reduction in false-positive authentication failures and a direct improvement in authentication pass rates, the foundational input for sustaining high Effective Inbox Placement in environments governed by increasingly sophisticated AI-based filtering.
Second, domain reputation protection against replay attacks. For platforms distributing newsletters and transactional notifications to large subscriber bases, cryptographically binding the signature to a specific set of recipients is a critical defensive layer. Intercepted, legitimately signed messages lose their utility as attack vectors, directly protecting the sending domain against unauthorized use and the reputational damage that follows.
Third, a fundamental shift in bounce profile and ESP infrastructure requirements. Standardized DKIM2 adoption will give major mailbox providers the cryptographic assurance needed to safely restore asynchronous DSN delivery in cases where they currently prefer deferrals or silent drops. For CPaaS platforms and ESPs, this means a significant and likely rapid increase in inbound bounce volume that needs to be planned for in 2026 and 2027 infrastructure roadmaps. Platforms currently relying on manual bounce handling or silently discarding a portion of inbound traffic need to begin capacity planning now.
Secure asynchronous DSN handling also carries a deeper implication for compliance operations. Because a bounce is routed to the server that physically handled the outbound message, ESPs gain cryptographically verified attribution: identifying precisely which sender in their infrastructure generated a complaint or rejection. Current list suppression and complaint-handling logic frequently relies on heuristics and inference. DKIM2 creates the conditions for considerably more precise and defensible implementation.
Fourth, new challenges for DMARC analytics. Envelope binding changes the data structure that feeds DMARC aggregate reports. Rendering a message’s path through multiple intermediary hops in a way that remains readable and actionable is a genuine product engineering challenge for monitoring tool vendors. Organizations using DMARC analytics platforms should engage their vendors early on DKIM2 readiness roadmaps.
The pace of standardization work is outrunning earlier projections. The working draft has reached version draft-ietf-dkim-dkim2-spec-01, and successful interoperability tests between independent production systems have already been completed.
That said, deployment timeline projections for authentication protocol rollouts warrant measured optimism. The historical precedents are instructive: SPF was first proposed in 2003, and DMARC has existed since 2012, yet strict enforcement policies remain the exception rather than the norm across the global domain landscape.
The conditions for faster DKIM2 adoption are, however, materially better than they were for either of those predecessors. The core DNS key infrastructure requires no changes. Industry anti-abuse coordination is more mature and better aligned. And the specification is being written by engineers who operate the infrastructure it will run on.
The most probable scenario: deployed code at major mailbox providers appears by end of 2026, with full ecosystem rollout extending through 2027-2028. The current working document expires formally in October 2026, requiring a new iteration to be published before that date. Companion documents, including DNS key specifications and architecture guidance, are being developed in parallel.
Yes. On April 22, 2026, draft-ietf-dmarc-arc-to-historic-00 was submitted, formally deprecating the ARC protocol and recommending its designation as a historic standard. This decision was driven by the market’s lack of consensus regarding a trust model between forwarding nodes. DKIM2 solves the problem of message modification in a rigorous and cryptographically verifiable manner. This eliminates the need to rely on subjective trust in intermediaries, ultimately rendering ARC obsolete.
No. The DNS namespace is unchanged. DKIM2 keys are stored under the same record structure as current DKIM keys. The specification architecture assumes a long period of parallel operation between the two standards. Migration will be evolutionary, not a hard cutover.
Not yet. The specification is still in active development and may change before the final RFC is published. What has changed is that the standard is no longer a distant concern. Interoperability tests between independent systems have succeeded, pilot deployments at major mailbox providers are planned for late 2026, and organizations building infrastructure strategies for 2026-2027 should treat DKIM2 support as a near-term planning requirement, not a long-term research item.
The DKIM2 specification does not modify DMARC or SPF protocol logic. However, the new DSN routing model and strict SMTP envelope binding have meaningful operational implications. They will affect SPF configuration for senders using variable envelope return path (VERP) addressing and dedicated bounce subdomains. These interactions should be reviewed with your email infrastructure provider during implementation planning.
The IETF DKIM Working Group publishes all working documents at: datatracker.ietf.org/wg/dkim/documents/. Active technical discussion takes place on the working group mailing list: [email protected].
DKIM2 is the first authentication protocol redesign in over a decade that addresses the structural problems of the email ecosystem in a unified, coherent way, simultaneously closing the forwarding signature breakage problem, the DSN routing gap, and the replay attack vector. The fact that the specification is being authored by engineers from Yahoo, Google, and Fastmail gives it an operational weight that goes well beyond a typical IETF working document.
For organizations running email at scale (transactional, marketing, or B2B), DKIM2 signals an environment in which sending domain reputation will be tied even more directly to the cryptographic quality and operational discipline of the underlying infrastructure. With first deployments at major mailbox providers projected for end of 2026, the organizations that build solid foundations now will enter the DKIM2 era without disruption.
This article is based on the IETF working draft draft-ietf-dkim-dkim2-spec-01 and the accompanying motivation document draft-gondwana-dkim2-motivation-00. The standard is under active development and may change before the final RFC is published.
We live in a world where your customers switch seamlessly between laptops, smartphones, and tablets. They navigate a complex digital ecosystem – checking emails, using mobile apps, and reacting...
We are delighted to announce that Vercom S.A., the company behind the EmailLabs project, has successfully completed the ISO 22301 certification process. This significant achievement underscores our commitment to...
EmailLabs, as part of the Vercom group, proudly announces its full commitment to aligning its ICT services with the latest cybersecurity standards. In response to dynamically changing regulations, the...
We are pleased to announce that MessageFlow, a product from the Vercom S.A. group, has received the prestigious CSA (Certified Senders Alliance) Certification. This recognition not only underscores the...
Best practices, Best practices, Email Authentication
TL;DR: Strategic Takeaways for C-Level and Marketing Leaders DKIM2 is not a minor DNS configuration update. It is a systemic response to two critical business problems: Replay attacks: scenarios...
AI, Antispam, Best practices, Deliverability
C-Level TL;DR: Strategic Takeaways Recipient consent as a foundation (Item 0): Sending email messages without explicit recipient consent (opt-in) poses a significant risk to your sending infrastructure. Attempting to...
AI, Antispam, Best practices, Deliverability
Executive TL;DR: Strategic Takeaways Deliverability Schism: The growing divide between sales automation technologies and the security standards enforced by major global mailbox providers (collectively referred to as MAGY) is...
Best practices, Best practices, Email Authentication
TL;DR: Strategic Takeaways for C-Level and Marketing Leaders DKIM2 is not a minor DNS configuration update. It is a systemic response to two critical business problems: Replay attacks: scenarios...
AI, Antispam, Best practices, Deliverability
C-Level TL;DR: Strategic Takeaways Recipient consent as a foundation (Item 0): Sending email messages without explicit recipient consent (opt-in) poses a significant risk to your sending infrastructure. Attempting to...
AI, Antispam, Best practices, Deliverability
Executive TL;DR: Strategic Takeaways Deliverability Schism: The growing divide between sales automation technologies and the security standards enforced by major global mailbox providers (collectively referred to as MAGY) is...
Modern email systems no longer treat the primary inbox as the default destination for every message. The final classification of an email is the result of a multistage evaluation...
Best practices, Maile marketingowe, Marketing E-mails, Transactional Emails
Mass email sending is a critical strategy for business owners, marketers, developers, and nonprofit managers looking to scale their outreach. Whether you are announcing a new product feature, distributing...
Best practices, Marketing E-mails
Customer feedback is the fuel for business growth, but gathering it effectively requires more than just a list of questions. Survey emails remain the most direct channel for understanding...
Best practices, Email Marketing, Pytania i odpowiedzi
Mail merge combines a template document with data to create personalized communications. This technique saves time by automatically generating individualized letters, emails, and labels without manual entry. What Is...
IT & Tech, Pytania i odpowiedzi, Technical
When an email travels from sender to recipient, it passes through several critical components of email infrastructure. At the heart of this journey sits the Mail Transfer Agent (MTA)...
Best practices, Deliverability, Google and Yahoo's Requirements, Pytania i odpowiedzi
The world of email marketing is constantly evolving, and leading mail service providers – Gmail, Yahoo, Microsoft, and Apple – regularly update their guidelines for senders. In recent years,...