
Although the term “return path” might seem self-explanatory, many companies aren’t familiar with the process it denotes.
Simply put, the return path is a hidden header that indicates where the system should send bounced messages. It also identifies where the email actually came from.
Also called the reverse path, envelope from, envelope sender, MAIL FROM, and bounce address, the return path address ensures you can collect and process bounces from your emails appropriately. It is a crucial component of tracking the success of your email campaigns and improving deliverability.
The most significant advantage of using this solution is convenience. With all bounced emails kept together and organized, you will have a much easier time completing your tasks and ensuring everything runs smoothly.
Let’s examine why online businesses should use a custom return path address for their messages and how you can take advantage of it in greater detail.
The return path is an SMTP address that is separate from your original sender address. While the latter is visible to other parties, generating familiarity between your company and the recipients, the former is typically invisible.
The primary purpose of the custom return address is to prevent bounce receipts from crowding your original sending inbox. It works in the background by interacting with email servers.
Let us explain.
Suppose you want to run a new email campaign. In that case, you will likely send out many emails. You may even plan to send messages to your entire email list.
Unfortunately, some of those messages will bounce back due to various reasons.
Without the return path header in place, either your company’s inbox will be flooded with “failed delivery” messages, or the email server will be confused, and you’ll never know about the existence of the bounce.
Either way, this situation can negatively affect your sending reputation.
An established return path solves this issue. During the validation process, it works in tandem with the DMARC, which checks, among others, if the domain in your “From” address matches the Return-Path (SPF alignment test).
If it does, the system validates your identity as a sender. As a result, your message has a higher chance of getting through filters set by inbox providers and reaching its destination.
And if your message gets bounced, it lands in your bounce address.
Maximize your email deliverability and security with EmailLabs!
At EmailLabs, we automatically create a return path for all our clients. This way, we are able to collect all bounced messages and present their statuses in our analytical panel. Those addresses that have a hard bounce, for example, go on our internal blacklist so that we do not re-send to them, protecting the sender’s reputation.

This is how the hardbounces report looks in the EmailLabs dashboard.
However, you’re free to customize your return path, starting with the PRO plan.
A clear, systematic return path is vital for sending consistent signals that servers can use to establish authenticity.
DMARC stands for Domain-Based Message Authentication, Reporting, and Conformance.
It is an email validation system created to detect and prevent phishing. In this illegal activity, cyber-criminals pose as legitimate companies to lure individuals into providing them with sensitive data.
DMARC controls what happens if a message fails SPF and DKIM authentication checks and provides reports containing lots of valuable information.
Setting up a custom return path that leads to a subdomain on your main domain can help you pass the DMARC validation process (domain alignment). Ultimately, it is a straightforward method to improve your email deliverability.
Besides comparing your sender and return path names, DMARC looks at a host of other factors before deciding to allow or reject your email.
SPF is a “path-based” authentication system that protects domains from spoofing. It stands for Sender Policy Framework.
Basically, SPF allows you to specify which email servers are permitted to send messages on behalf of your domain. The mail server compares approved IP addresses to the IP address that sent the message. If the sender’s IP is among the approved IP, the email passes SPF authentication. If it fails, the message is treated as spam.
Using this system is crucial to prevent your emails from being marked as spam by receiving servers.
Usually, the best way to achieve SPF alignment is by using a custom return path address in the email header.
DKIM (Domain Keys Identified Mail) is yet another authentication method to protect you and your customers from spoofing and phishing.
How does it work? Sending server signs the email using a private key. The receiving server verifies whether messages are authentic by using the public key (DKIM entry placed in DNS).
If the DKIM validation passes, the receiving server can be confident the message was sent by the address in the Return Path and wasn’t altered in transit.
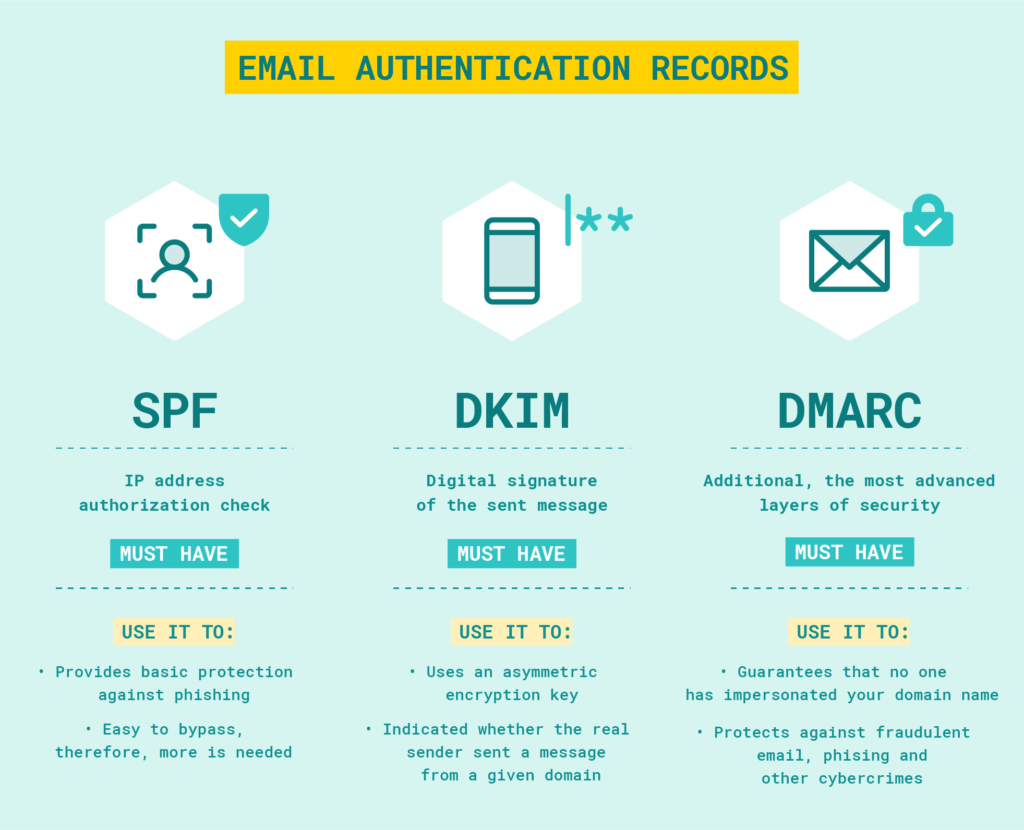
SPF, DKIM, DMARC: Basic elements of email authentication
More often than not, dealing with bounced messages is a headache. Even if you run a small company, the number of emails in your inbox can quickly pile up.
Using a customized return path header can help you with that problem. Plus, it is vital for email authentication processes.
As outlined above, it allows the recipient’s server to determine whether the email comes from a verified source. It is crucial for DKIM, DMARC, and SPF alignment. Without it, your messages can get rejected, damaging your email deliverability and sender score.
Additionally, the return path keeps your original sending inbox free from unnecessary clutter. Thanks to it, you can focus on what matters most and attend to email errors whenever it suits you.
Maximize your email deliverability and security with EmailLabs!
When you send emails from your webmail (e.g. Google, Hotmail, Yahoo), the Return Path is normally set to send bounces back to your personal email address. Email Service Provider (e.g., EmailLabs) on the other hand, automatically adds the return path header for their customers. This way, they can detect problems regarding delivering the messages and resolve some of them.
That being said, you can contact your ESP to create a custom return path for your messages. Doing so can help you send consistent signals in your emails, significantly boosting your deliverability.
Cleaning up your email header and customizing your return path is crucial to maintaining a high sending reputation and ensuring your emails will pass the validations performed by mailbox providers.
The most straightforward method to set up a custom return path is to contact your email provider and ask if they support setting a custom Return Path as the setup instructions will vary between different providers.
Contact us to learn how we can help you!
Alternatively, you can do most of the heavy lifting yourself.
You can set your own Return Path using the EmailLabs admin panel or with help from our experts.
Setting up a custom Return Path in EmailLabs is quick and easy to implement using one of the two following methods:
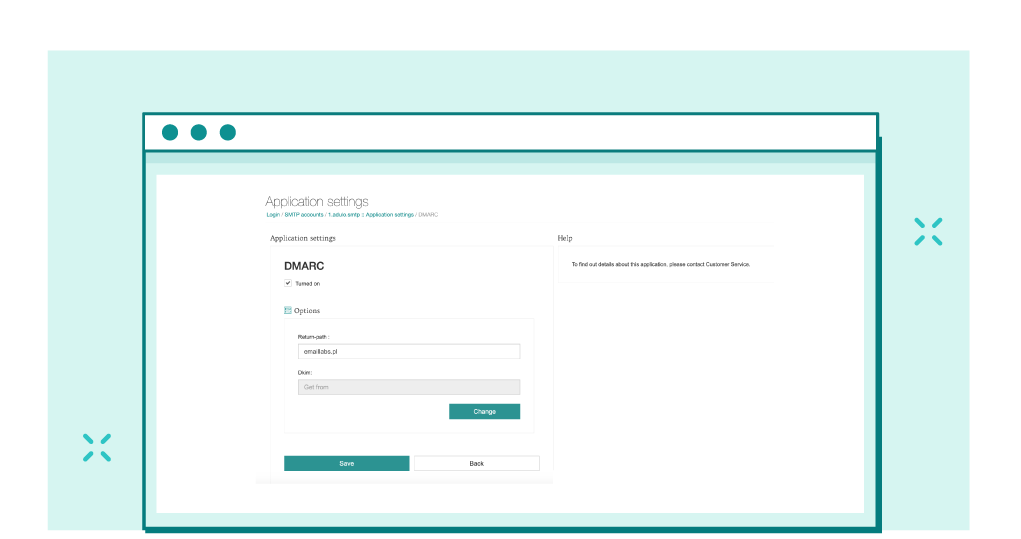
1. Return Path in the DMARC application
The chosen domain that matches from address must be entered in the EmailLabs panel (SMTP Accounts > Settings > DMARC: Turned on).
Please note that up to 2% of the bounced messages may be directed to your domain. These bounces are returned by the receiving servers to the domain set in the Return Path field. The remaining 98% of the bounces are passed to EmailLabs in an SMTP session during the server_smtp – server_smtp communication. This means that some of the information regarding undelivered messages may come to your domain directly.
This method is not recommended for senders using multiple sending domains.
2. Disabling Return Path overwriting by EmailLabs.
Create a subdomain from your sending domain, such as bounce.mydomain.com. It is important that no current mail is handled on such a subdomain. Then it will be possible to set up our MX records, which will enable us to collect 100% of bounces from receiving servers and present the data in the Emaillabs panel.
Publish both MX records to the DNS server of the custom Return Path domain, for example:
Domain: bounce.mydomain.com
Entry type: MX
Value: bounce01.emaillabs.net.pl
and
Domain: bounce.mydomain.com
Entry type: MX
Value: bounce02.emaillabs.net.pl
Then please contact our Support Team to disable Return Path overwriting.
Both methods are available starting with PRO Plan.
We live in a world where your customers switch seamlessly between laptops, smartphones, and tablets. They navigate a complex digital ecosystem – checking emails, using mobile apps, and reacting...
We are delighted to announce that Vercom S.A., the company behind the EmailLabs project, has successfully completed the ISO 22301 certification process. This significant achievement underscores our commitment to...
EmailLabs, as part of the Vercom group, proudly announces its full commitment to aligning its ICT services with the latest cybersecurity standards. In response to dynamically changing regulations, the...
We are pleased to announce that MessageFlow, a product from the Vercom S.A. group, has received the prestigious CSA (Certified Senders Alliance) Certification. This recognition not only underscores the...
Compliance & Security, Email Marketing, Security
TL;DR DMARCbis is now official: After years of work by the IETF working group, the DMARC specification has been formally updated. Three new documents, RFC 9989, RFC 9990, and...
Email Marketing, Gmail, New feature
TL;DR Gmail Live: a new feature enabling natural language voice search in the inbox, powered by the Gemini model. AI Inbox and AI Overviews: a revamped inbox interface featuring...
Best practices, Best practices, Email Authentication
TL;DR: Strategic Takeaways for C-Level and Marketing Leaders DKIM2 is not a minor DNS configuration update. It is a systemic response to two critical business problems: Replay attacks: scenarios...
Compliance & Security, Email Marketing, Security
TL;DR DMARCbis is now official: After years of work by the IETF working group, the DMARC specification has been formally updated. Three new documents, RFC 9989, RFC 9990, and...
Email Marketing, Gmail, New feature
TL;DR Gmail Live: a new feature enabling natural language voice search in the inbox, powered by the Gemini model. AI Inbox and AI Overviews: a revamped inbox interface featuring...
Best practices, Best practices, Email Authentication
TL;DR: Strategic Takeaways for C-Level and Marketing Leaders DKIM2 is not a minor DNS configuration update. It is a systemic response to two critical business problems: Replay attacks: scenarios...
AI, Antispam, Best practices, Deliverability
C-Level TL;DR: Strategic Takeaways Recipient consent as a foundation (Item 0): Sending email messages without explicit recipient consent (opt-in) poses a significant risk to your sending infrastructure. Attempting to...
AI, Antispam, Best practices, Deliverability
Executive TL;DR: Strategic Takeaways Deliverability Schism: The growing divide between sales automation technologies and the security standards enforced by major global mailbox providers (collectively referred to as MAGY) is...
Modern email systems no longer treat the primary inbox as the default destination for every message. The final classification of an email is the result of a multistage evaluation...
Best practices, Maile marketingowe, Marketing E-mails, Transactional Emails
Mass email sending is a critical strategy for business owners, marketers, developers, and nonprofit managers looking to scale their outreach. Whether you are announcing a new product feature, distributing...
Best practices, Marketing E-mails
Customer feedback is the fuel for business growth, but gathering it effectively requires more than just a list of questions. Survey emails remain the most direct channel for understanding...
Best practices, Email Marketing, Pytania i odpowiedzi
Mail merge combines a template document with data to create personalized communications. This technique saves time by automatically generating individualized letters, emails, and labels without manual entry. What Is...